Our Blog
“Welcome to the CISTCK Group Cybersecurity Blog! Dive into the dynamic world of cybersecurity with our expert insights, thought-provoking articles, and the latest developments in the field. Our blog is your go-to resource for staying ahead in the ever-evolving landscape of cyber threats. Explore topics ranging from threat intelligence and risk management to industry best practices and emerging technologies. Whether you’re a cybersecurity professional, IT enthusiast, or simply interested in safeguarding digital landscapes, join us on a journey of knowledge-sharing and discover actionable strategies to fortify your defenses. Stay informed, stay secure with the CISTCK Group Cybersecurity Blog.”

Latrodectus Malware Loader Emerges as IcedID’s Successor in Phishing Campaigns
Cybersecurity researchers have observed a spike in email phishing campaigns starting early March 2024 that delivers Latrodectus, a nascent malware loader believed to be the successor to the IcedID malware. "These campaigns typically involve a recognizable infection...

Chinese Nationals Arrested for Laundering $73 Million in Pig Butchering Crypto Scam
The U.S. Department of Justice (DoJ) has charged two arrested Chinese nationals for allegedly orchestrating a pig butchering scam that laundered at least $73 million from victims through shell companies. The individuals, Daren Li, 41, and Yicheng Zhang, 38, were...

Grandoreiro Banking Trojan Resurfaces, Targeting Over 1,500 Banks Worldwide
The threat actors behind the Windows-based Grandoreiro banking trojan have returned in a global campaign since March 2024 following a law enforcement takedown in January. The large-scale phishing attacks, likely facilitated by other cybercriminals via a...
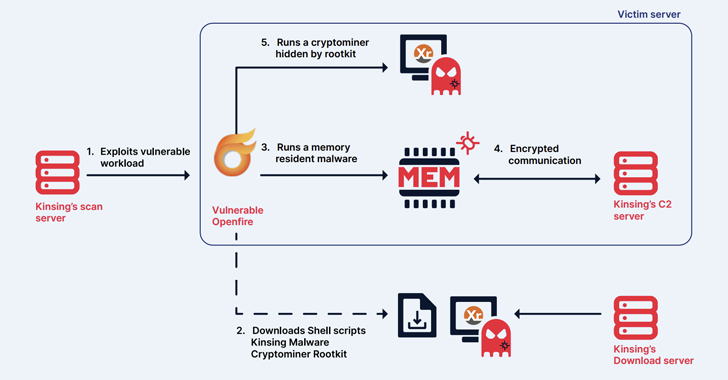
Kinsing Hacker Group Exploits More Flaws to Expand Botnet for Cryptojacking
The cryptojacking group known as Kinsing has demonstrated its ability to continuously evolve and adapt, proving to be a persistent threat by swiftly integrating newly disclosed vulnerabilities to exploit arsenal and expand its botnet. The findings come from cloud...

New XM Cyber Research: 80% of Exposures from Misconfigurations, Less Than 1% from CVEs
A new report from XM Cyber has found – among other insights - a dramatic gap between where most organizations focus their security efforts, and where the most serious threats actually reside. The new report, Navigating the Paths of Risk: The State of Exposure...
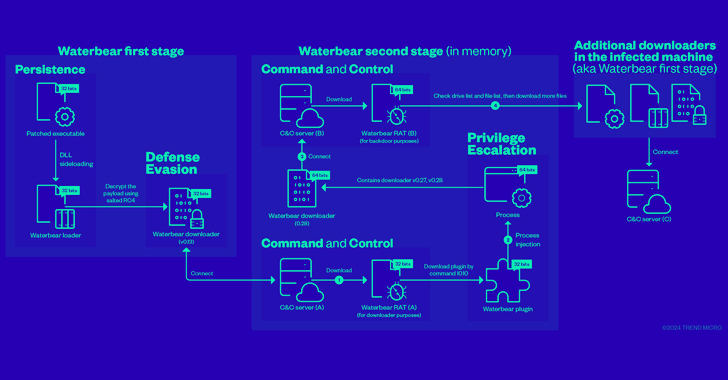
China-Linked Hackers Adopt Two-Stage Infection Tactic to Deploy Deuterbear RAT
Cybersecurity researchers have shed more light on a remote access trojan (RAT) known as Deuterbear used by the China-linked BlackTech hacking group as part of a cyber espionage campaign targeting the Asia-Pacific region this year. "Deuterbear, while similar to...
Kimsuky APT Deploying Linux Backdoor Gomir in South Korean Cyber Attacks
The Kimsuky (aka Springtail) advanced persistent threat (APT) group, which is linked to North Korea's Reconnaissance General Bureau (RGB), has been observed deploying a Linux version of its GoBear backdoor as part of a campaign targeting South Korean organizations....

CISA Warns of Actively Exploited D-Link Router Vulnerabilities – Patch Now
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Thursday added two security flaws impacting D-Link routers to its Known Exploited Vulnerabilities (KEV) catalog, based on evidence of active exploitation. The list of vulnerabilities is as follows -...

New Wi-Fi Vulnerability Enables Network Eavesdropping via Downgrade Attacks
Researchers have discovered a new security vulnerability stemming from a design flaw in the IEEE 802.11 Wi-Fi standard that tricks victims into connecting to a less secure wireless network and eavesdrop on their network traffic. The SSID Confusion attack, tracked as...
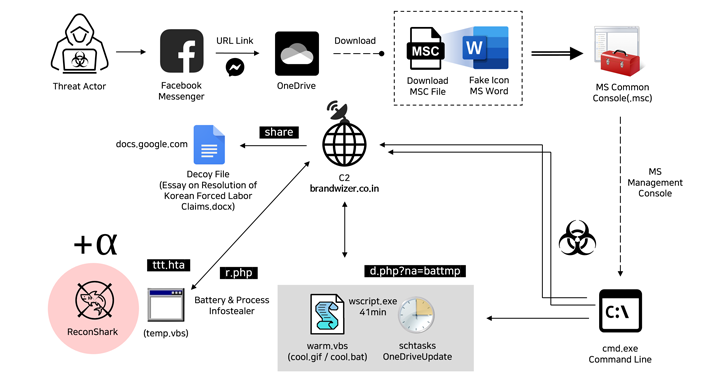
North Korean Hackers Exploit Facebook Messenger in Targeted Malware Campaign
The North Korea-linked Kimsuky hacking group has been attributed to a new social engineering attack that employs fictitious Facebook accounts to targets via Messenger and ultimately delivers malware. "The threat actor created a Facebook account with a fake identity...
