Our Blog
“Welcome to the CISTCK Group Cybersecurity Blog! Dive into the dynamic world of cybersecurity with our expert insights, thought-provoking articles, and the latest developments in the field. Our blog is your go-to resource for staying ahead in the ever-evolving landscape of cyber threats. Explore topics ranging from threat intelligence and risk management to industry best practices and emerging technologies. Whether you’re a cybersecurity professional, IT enthusiast, or simply interested in safeguarding digital landscapes, join us on a journey of knowledge-sharing and discover actionable strategies to fortify your defenses. Stay informed, stay secure with the CISTCK Group Cybersecurity Blog.”
Bogus npm Packages Used to Trick Software Developers into Installing Malware
An ongoing social engineering campaign is targeting software developers with bogus npm packages under the guise of a job interview to trick them into downloading a Python backdoor. Cybersecurity firm Securonix is tracking the activity under the...

Severe Flaws Disclosed in Brocade SANnav SAN Management Software
Several security vulnerabilities disclosed in Brocade SANnav storage area network (SAN) management application could be exploited to compromise susceptible appliances. The 18 flaws impact all versions up to and including 2.3.0, according to independent security...

10 Critical Endpoint Security Tips You Should Know
In today's digital world, where connectivity is rules all, endpoints serve as the gateway to a business’s digital kingdom. And because of this, endpoints are one of hackers' favorite targets. According to the IDC, 70% of successful breaches start at the endpoint....
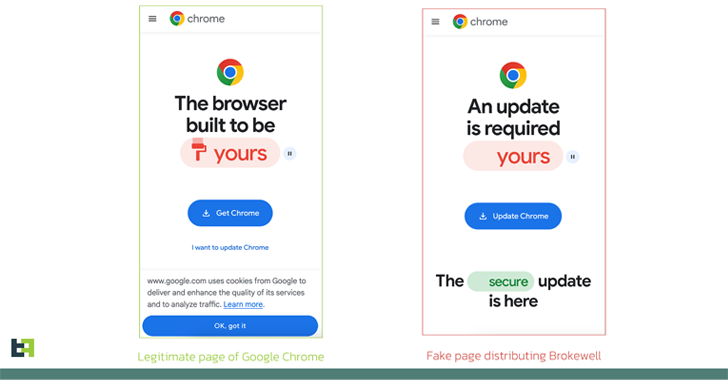
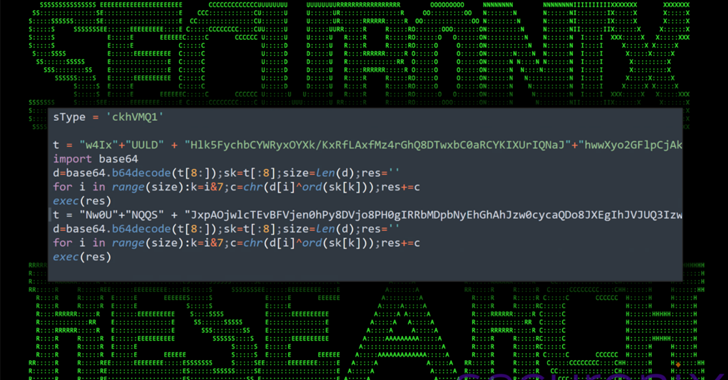
New ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
Fake browser updates are being used to push a previously undocumented Android malware called Brokewell. "Brokewell is a typical modern banking malware equipped with both data-stealing and remote-control capabilities built into the malware," Dutch security firm...

Palo Alto Networks Outlines Remediation for Critical PAN-OS Flaw Under Attack
Palo Alto Networks has shared remediation guidance for a recently disclosed critical security flaw impacting PAN-OS that has come under active exploitation. The vulnerability, tracked as CVE-2024-3400 (CVSS score: 10.0), could be weaponized to obtain unauthenticated...

Hackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
Threat actors are attempting to actively exploit a critical security flaw in the WP‑Automatic plugin for WordPress that could allow site takeovers. The shortcoming, tracked as CVE-2024-27956, carries a CVSS score of 9.9 out of a maximum of 10. It impacts all versions...

North Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
The North Korea-linked threat actor known as Lazarus Group employed its time-tested fabricated job lures to deliver a new remote access trojan called Kaolin RAT. The malware could, "aside from standard RAT functionality, change the last write timestamp of a selected...

Network Threats: A Step-by-Step Attack Demonstration
Follow this real-life network attack simulation, covering 6 steps from Initial Access to Data Exfiltration. See how attackers remain undetected with the simplest tools and why you need multiple choke points in your defense strategy. Surprisingly, most network attacks...

DOJ Arrests Founders of Crypto Mixer Samourai for $2 Billion in Illegal Transactions
The U.S. Department of Justice (DoJ) on Wednesday announced the arrest of two co-founders of a cryptocurrency mixer called Samourai and seized the service for allegedly facilitating over $2 billion in illegal transactions and for laundering more than $100 million in...

Google Postpones Third-Party Cookie Deprecation Amid U.K. Regulatory Scrutiny
Google has once again pushed its plans to deprecate third-party tracking cookies in its Chrome web browser as it works to address outstanding competition concerns from U.K. regulators over its Privacy Sandbox initiative. The tech giant said it's working closely with...
